Descope Alternatives in 2026 for B2B Agentic Apps

Where Descope Creates Friction for B2B AI Apps
Descope's flow-based model is well-suited for teams that want to configure auth behavior visually. For B2B AI products, the friction is structural.
The visual editor is the abstraction layer — and the constraint. Descope's model requires builders to configure flows for behaviors that org-first platforms handle natively: per-org domain routing, org-level role assignment, org hierarchy. Each is achievable, but through flow construction rather than out-of-the-box behavior. As product complexity grows — agents acting on behalf of orgs, MCP servers per customer, enterprise provisioning per tenant — maintaining those flows becomes operational work that purpose-built platforms absorb natively.
Pricing scales across multiple meters simultaneously. Descope charges on MAUs, tenant count, SSO connections, SCIM connections, and M2M exchanges — where M2M exchanges include token exchanges for machine-to-machine flows and MCP authentication scenarios. For a pure AI agent product with high M2M traffic and a growing enterprise customer base, costs compound across several dimensions at once. Third-party reviews have cited enterprise quotes reaching $80K/year at larger scale.
Pricing (based on the shared scenario): The shared scenario — 200 orgs, 8,000 MAUs, 50 SSO connections — exceeds Descope's Growth tier (capped at 25,000 MAUs, 100 tenants, and 10 SSO connections at $799/month) and lands in Enterprise custom pricing. Published SSO overage rates are approximately $50/connection/month on paid tiers. Estimated monthly total: $3,000–$4,000+/month, subject to negotiation. M2M exchange billing for agent workloads adds further cost depending on token volume.
1. Scalekit
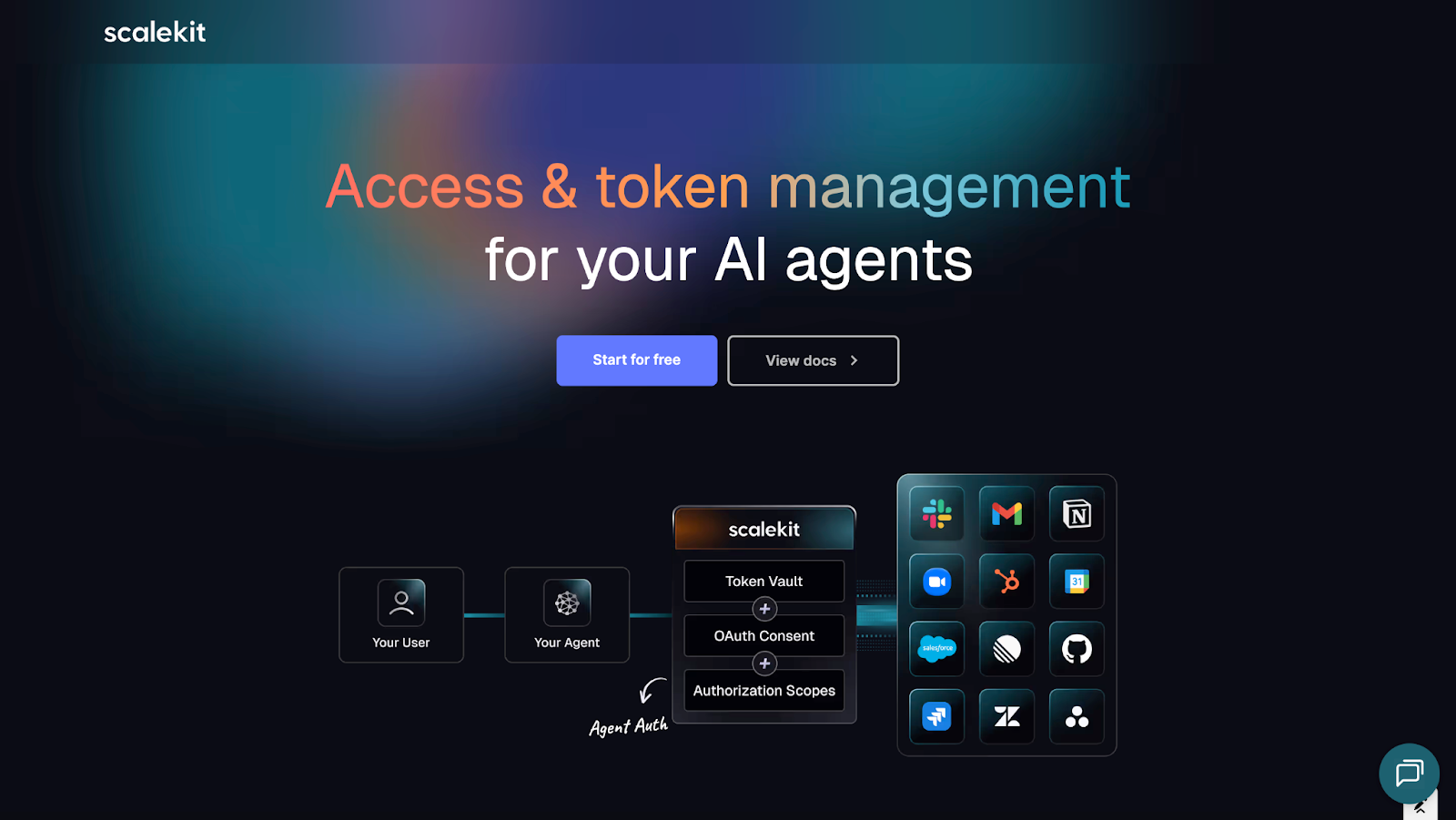
Enterprise readiness credentials: Scalekit is the auth stack built for B2B AI applications. Organizations are the root identity object. Every user, agent, and MCP server operates within the context of an organization — that's an architectural assumption, not a feature addition.
For pure AI agent products, Scalekit is built around delegated access: agents take actions, make tool calls, and execute workflows on behalf of users and organizations across 100+ prebuilt connectors. Access is user-approved via OAuth, tokens are scoped and short-lived, auto-rotation is handled by the platform, and every agent action produces an audit trail tied to the org and the user who granted access. There is no ambiguity about what an agent did, on whose behalf, and under what permissions.
MCP Auth secures remote MCP servers with drop-in OAuth 2.1 — Dynamic Client Registration, Client ID Metadata Documents, PKCE flows, tool-level scopes, and built-in consent screens — so the same delegated access model applies when AI clients connect to your product's MCP server.
Enterprise SSO supports SAML and OIDC across Okta, Microsoft Entra ID, Google Workspace, JumpCloud, OneLogin, AD FS, PingIdentity, Shibboleth, and generic SAML/OIDC connections. One integration covers every enterprise identity provider your customers will ask for. SCIM provisioning handles automated user provisioning, deprovisioning, group-to-role mapping, custom attribute sync, and real-time webhooks. A self-service Admin Portal lets customer IT teams configure their own SSO and SCIM connections through a branded, embeddable interface.
Where Scalekit Differs from Descope for B2B AI
Org-first by architecture, not configuration. Scalekit is built around organizations as the root object. Users, agents, and machines always resolve in the context of an org. Descope is user-first; org context requires configuration.
Delegated access and agent actions as platform primitives. Tool calls, agent actions, and third-party integrations run through a managed token vault with scoped retrieval permissions, auto-rotation, and org-level access controls — not flows that need to be configured and maintained.
Audit trails for agents, included. Every agent action taken on behalf of a user or org is logged with full context: which org, which user granted access, which tool was called, and under what scope. This is built into the platform, not a separate logging concern.
No separate M2M metering at standard tiers. For AI agent products with high token exchange volume, Scalekit's pricing model does not compound a separate M2M dimension on top of MAU, connection, and tenant charges.
Modular adoption. Scalekit sits alongside Auth0, Firebase, Cognito, or any existing auth system. MCP Auth or Agent Auth can be added first, without migrating users or replacing sessions. Teams expand to full-stack auth — users, orgs, RBAC — when the time is right.
Built-in IdP Simulator. Every Scalekit account includes an IdP Simulator. Teams validate SSO flows, test error scenarios, and debug edge cases before a single enterprise customer touches the login page. No manual IdP configuration for testing.
Full auth logs, included. Rich auth log payloads with complete request-level detail are included in every account. Debugging auth does not require a plan upgrade.
Pricing
Estimated monthly cost (shared scenario): ~$2,085–$2,340/month for SSO + SCIM at 50 connections each.
2. WorkOS
Enterprise readiness credentials: WorkOS made a deliberate architectural choice: focus on enterprise authentication capabilities — SAML SSO, SCIM provisioning, directory sync — and expose them as a clean, developer-friendly API layer. The Admin Portal is polished. The SAML implementation is thorough. Documentation quality is consistently rated as one of the strongest in the category. OpenAI, Cursor, and Perplexity are among its production customers.
WorkOS has since expanded into user management (AuthKit), MCP Auth, and Pipes for agent connectors, building on top of that enterprise-auth foundation.
Where Friction Appears
WorkOS is designed as an enterprise auth layer to sit alongside a primary user auth system, not as a unified platform. As product surfaces multiply — human users, agents, MCP servers, M2M — operating a split identity layer requires more coordination. Agent identity and MCP server security are more recent additions; enterprise SSO and SCIM remain the flagship.
Auth log detail is limited on the default plan. There is no built-in IdP Simulator. At 50 SSO + SCIM connections, per-connection pricing compounds significantly.
Pricing (based on the shared scenario):
WorkOS charges $125/connection/month for SSO, with volume tiers: $100/month for connections 16–30, $80/month for connections 31–50. SCIM mirrors the same structure.
- SSO (50 connections): (15 × $125) + (15 × $100) + (20 × $80) = $4,975/month
- SCIM (50 connections): same = $4,975/month
- Estimated monthly total: ~$9,950/month — not including primary auth system cost or custom domains
3. Auth0
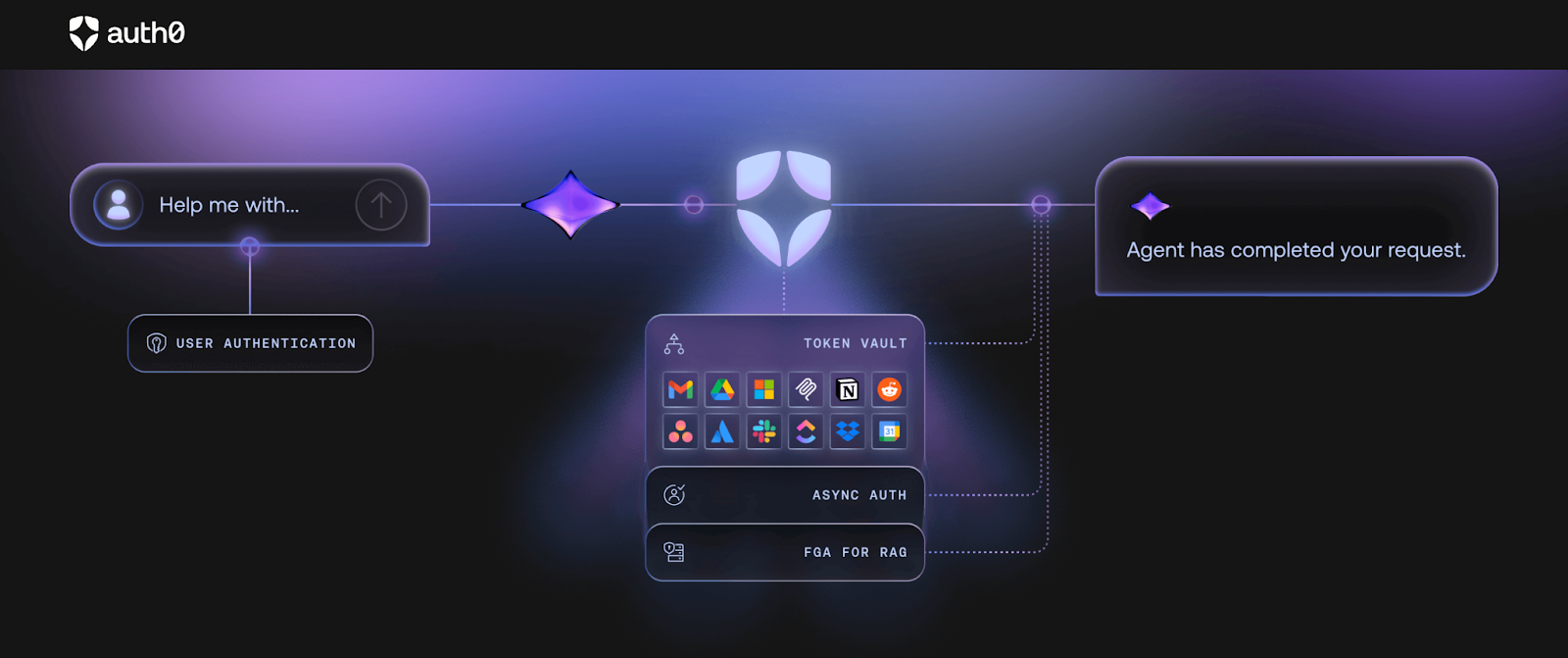
Enterprise readiness credentials: Auth0 is the most established name in authentication. It supports enterprise SSO through the Organizations feature, with SAML and OIDC connections to major identity providers.
Where Friction Appears
The architecture is user-first. B2B organizational modeling is layered on top of a user-centric model rather than native to it. Non-human actors — agents, background jobs, MCP servers — are not modeled as distinct identity types; they're handled via application clients or custom logic.
Enterprise SSO is gated behind higher-tier plans. The B2B Essentials plan ($150/month) includes 3 SSO connections. The Professional plan ($800/month) adds 2 more. Beyond 5 connections, teams engage sales. Each environment requires a separate tenant, which means paying for the same user base multiple times. For pure AI agent products, the combination of MAU-based billing, per-connection gating, and the need to reconstruct org context and agent identity in application code makes costs and complexity compound together.
Estimated monthly cost (shared scenario): ~$3,500–$6,000+/month. Requires sales engagement at this scale.
4. Clerk
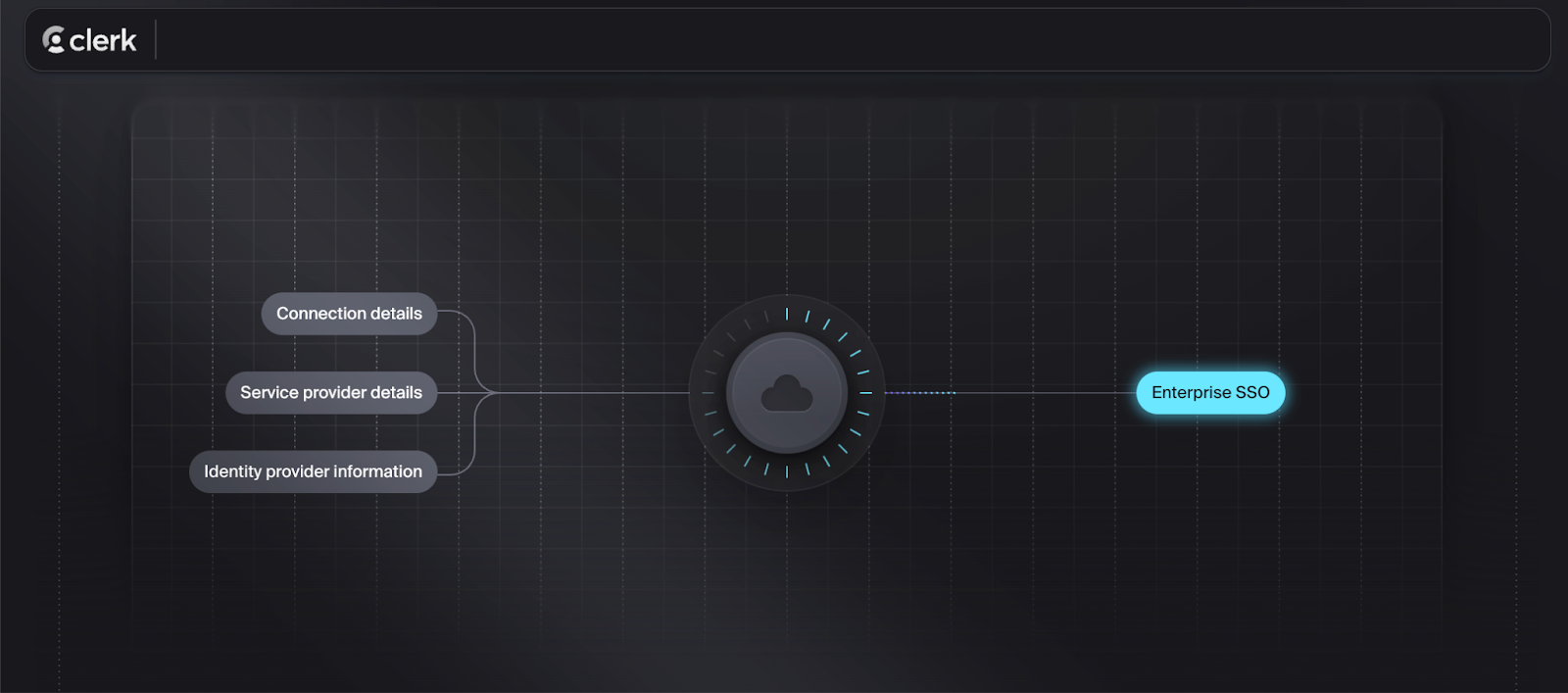
Enterprise readiness credentials: Clerk's developer experience for user authentication is notable. Drop-in React components, fast path to a working login page, and SDK quality that few platforms approach. B2B Organizations, multi-tenancy, enterprise SSO (SAML and OIDC), and RBAC are all available but are limited in maturity. SCIM is not supported out-of-the-box.
Where Friction Appears
Organizations in Clerk are groupings of users rather than the root identity boundary. SCIM provisioning is not natively supported — for enterprise customers whose IT teams require automated directory sync, this is a procurement blocker. Clerk does not provide a self-service Admin Portal where customer IT teams configure their own SSO connections; setup falls on your engineering team.
Non-human actors — agents, background jobs, MCP servers — are not modeled as distinct identity types. For pure AI agent products requiring org-scoped agent identity and MCP server security, significant application-level work is required.
Pricing (based on the shared scenario):
- 8,000 MAUs within free tier = $0
- 200 orgs: (200 - 100) × $1 = $100/month
- Enhanced Authentication add-on (SSO): $100/month
- Enhanced Organizations add-on (SCIM unavailable natively)
- Estimated monthly total: ~$200–$300/month for base scenario. Enterprise SSO at 50 separate configurations requires custom pricing not publicly available. SCIM is not available without external tooling.
5. Cognito
Enterprise readiness credentials: Amazon Cognito is the foundation for teams already deeply embedded in AWS infrastructure. User Pools handle user auth; Identity Pools handle federation. Pricing is among the lowest in the category at standard MAU volumes, and AWS ecosystem integration is unmatched for teams already running on AWS.
Where Friction Appears
Cognito provides low-level primitives. Organizations, per-org SSO configuration, customer-facing admin UX, SCIM provisioning, agent identity, and MCP server security are all implementation work. For teams with strong AWS infrastructure expertise and engineering capacity, it can be cost-effective. For teams that need enterprise SSO, SCIM, and agent auth to work without significant custom development, it is not a managed solution.
Estimated monthly cost (shared scenario): ~$0–$50/month for the platform itself. Engineering cost to build and maintain the B2B and AI-identity layer on top is the real expense.
6. FusionAuth
Enterprise readiness credentials: FusionAuth is a full-featured identity platform that supports self-hosting, private cloud, or managed cloud deployment. It supports OAuth 2.0, OIDC, SAML, and SCIM, and covers a broad set of enterprise auth features. For teams with data residency requirements, compliance constraints requiring on-premise deployment, or a preference for owning identity infrastructure, FusionAuth is one of the few platforms that supports all three deployment models.
Where Friction Appears
Self-hosting means infrastructure operations, upgrade management, and uptime ownership fall to your team. B2B-native abstractions — per-org SSO configuration, org-scoped authorization, agent identity — are available but require configuration and, in some cases, custom development. FusionAuth is not a B2B AI-native platform by design.
Estimated monthly cost (shared scenario): ~$250–$500+/month for cloud-hosted Essentials. Self-hosted Community edition is free; Enterprise edition requires a negotiated license. Exact cost depends on deployment model and features needed.
7. PropelAuth
Enterprise readiness credentials: PropelAuth is built exclusively for B2B products. Organizations are a native construct. SSO, SCIM, RBAC, API key management, and a hosted org management UI are included in paid tiers without per-connection gating. The Growth plan at $150/month includes unlimited SSO connections; SCIM requires the Growth Plus plan at $500/month. MCP authentication is listed as a supported feature.
Where Friction Appears
PropelAuth is a hosted, opinionated platform. Teams that need fine-grained control over auth UI, custom token structures, or deep integration with existing infrastructure find the hosted model limiting. Agent identity and MCP server security beyond basic MCP auth support are not first-class platform primitives. Customization options are narrower than API-first platforms.
Estimated monthly cost (shared scenario):
- Growth Plus plan: $500/month
- Unlimited SSO connections included
- SCIM included at Growth Plus
- 8,000 MAUs within 10,000 free user limit = $0 extra
- Estimated monthly total: ~$500/month
PropelAuth's per-connection-unlimited approach makes it one of the most cost-effective options for teams whose primary requirement is enterprise SSO and SCIM without heavy customization or purpose-built agent auth.
Decision Framework
FAQs
Is Descope suitable for B2B AI apps?
Descope covers standard B2B auth requirements — SSO, SCIM, MFA, passwordless — and has added agentic identity capabilities through its Agentic Identity Hub (launched 2025). Teams building pure AI agent products with high M2M token volume and many enterprise customers may find that pricing compounds quickly across multiple billing dimensions, and that org-first and agent identity behaviors require more flow configuration than on purpose-built platforms.
Do I need to replace my existing auth system to adopt an alternative?
Not necessarily. Several platforms on this list — including Scalekit and WorkOS — are designed to sit alongside an existing user auth system. SSO, SCIM, MCP Auth, or Agent Auth can be added incrementally without migrating users or replacing sessions.
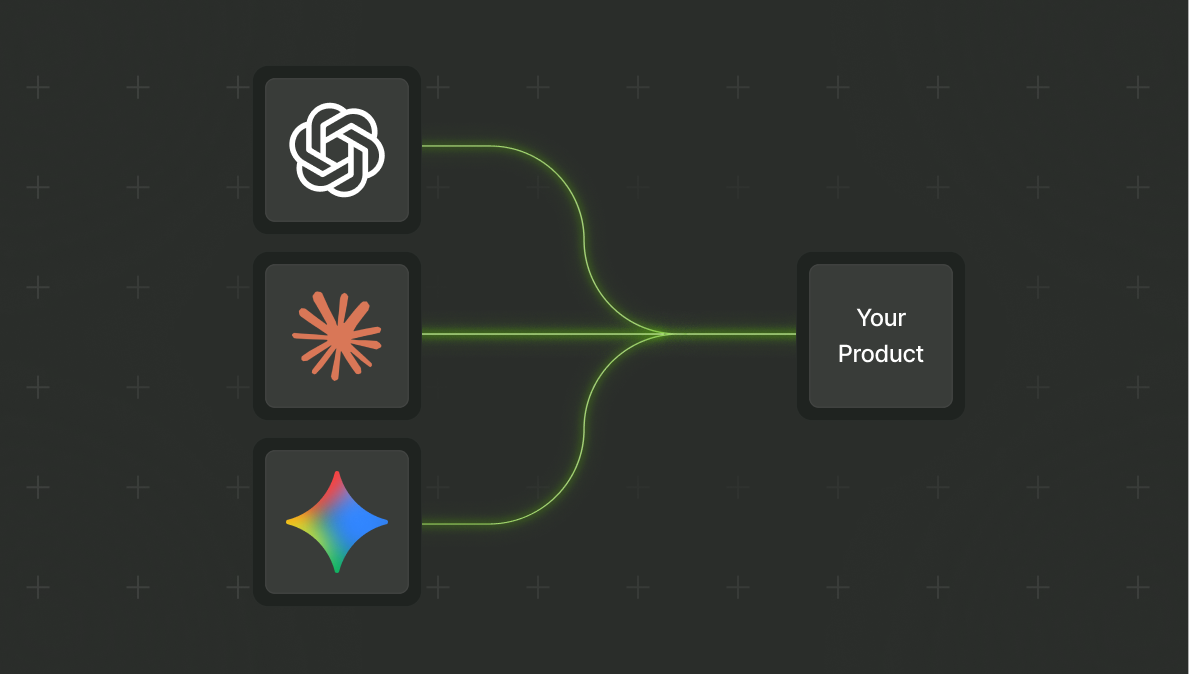
What makes an auth platform suitable for AI agent products specifically?
The key questions are whether organizations are a native identity boundary (not a configuration layer), whether agent and machine actors are modeled explicitly as identity types, and whether delegated access — tool calls and agent actions on behalf of users — produces auditable, org-scoped tokens rather than relying on application-level workarounds.
How should I evaluate pricing across these platforms?
Model against your expected enterprise customer count in 12 months, not today. The platforms on this list use different pricing dimensions — per-connection, per-MAU, per-tenant, per-M2M-exchange, or flat-tier. Running the same scenario across all of them is the only way to compare like-for-like.












