







































































Auth0 is reliable and flexible. The challenge is architectural: as execution paths multiply, agents, APIs, MCP servers, background jobs, more identity logic tends to move into application code rather than being enforced centrally. You'll soon find your engineers spending time on identity plumbing instead of your roadmap, while costs multiply.
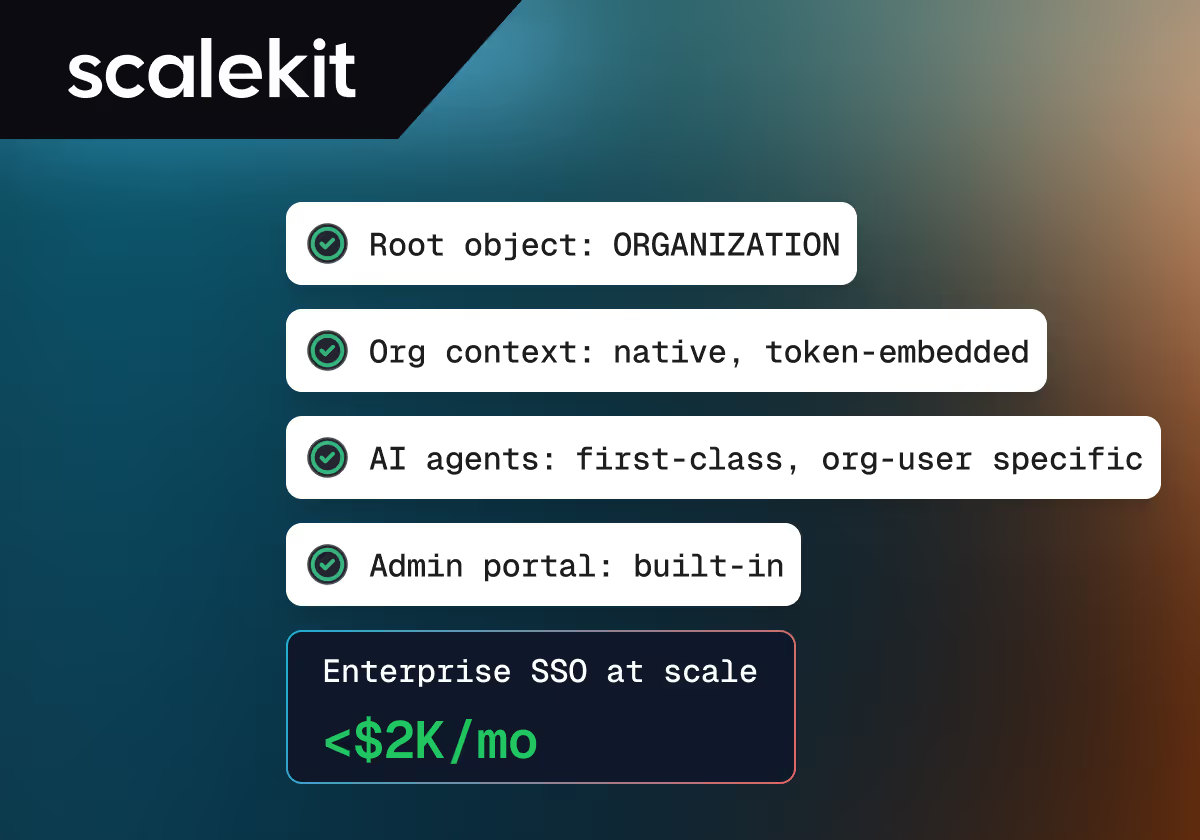
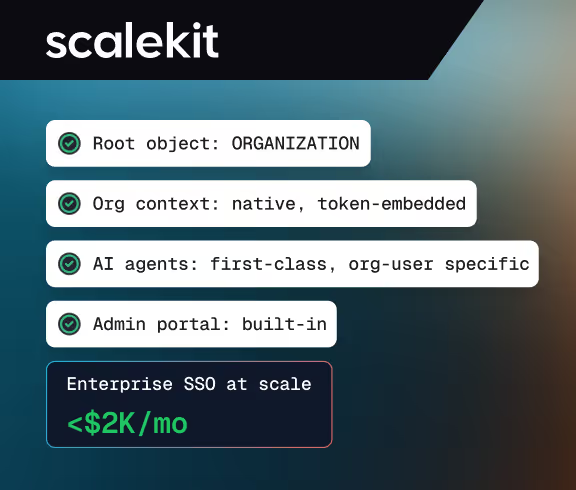
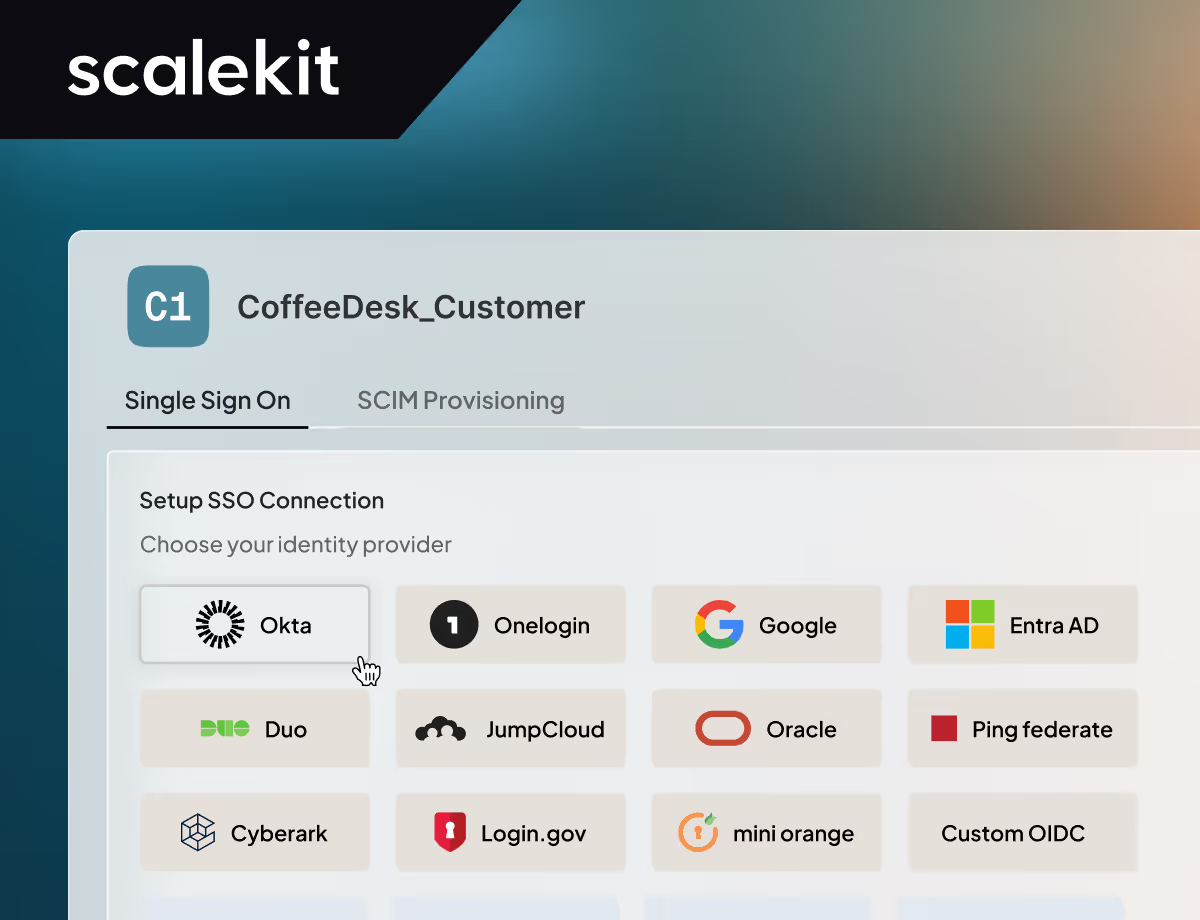
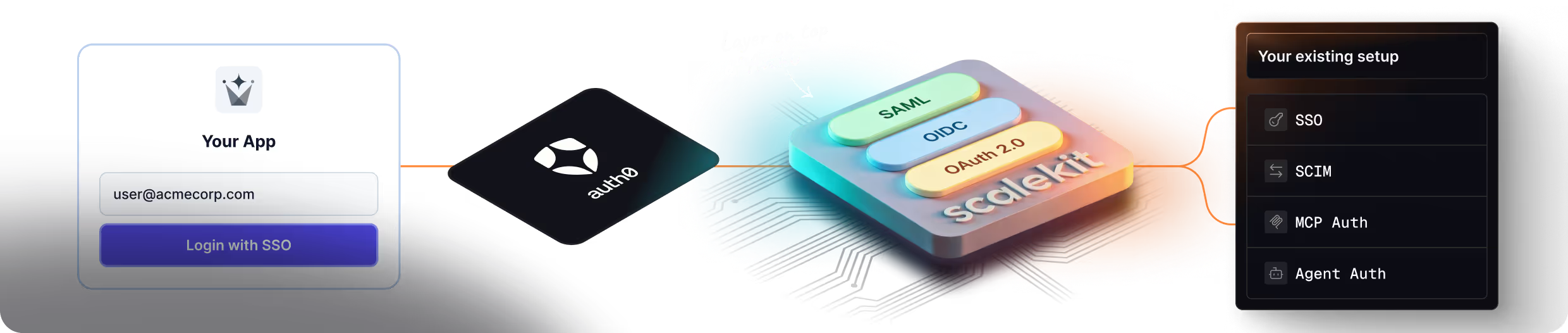
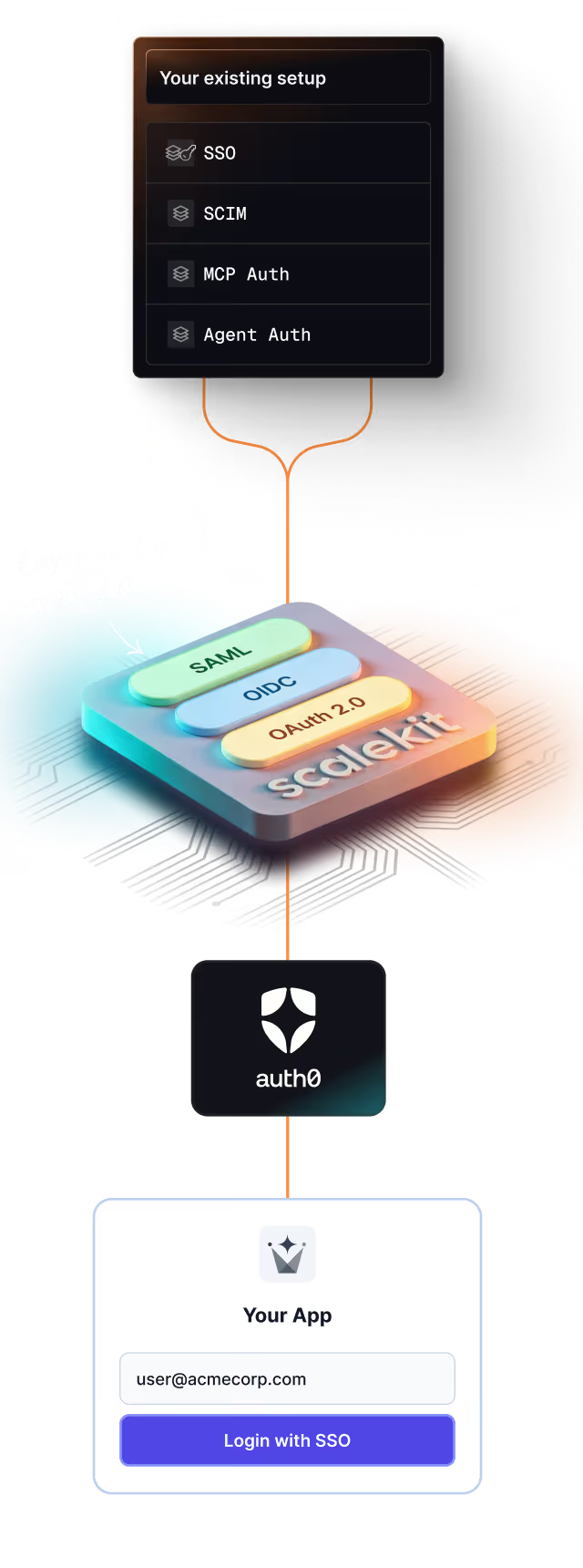
You don't replace Auth0 on day one. Most teams introduce Scalekit alongside it; starting with enterprise SSO and SCIM, or agent and MCP auth, while leaving user login on Auth0. Existing users map naturally into org memberships. Migration happens capability by capability, without breaking sessions or tokens. For Full stack migration, refer to this guide or get a Scalekit engineer to help you get started.
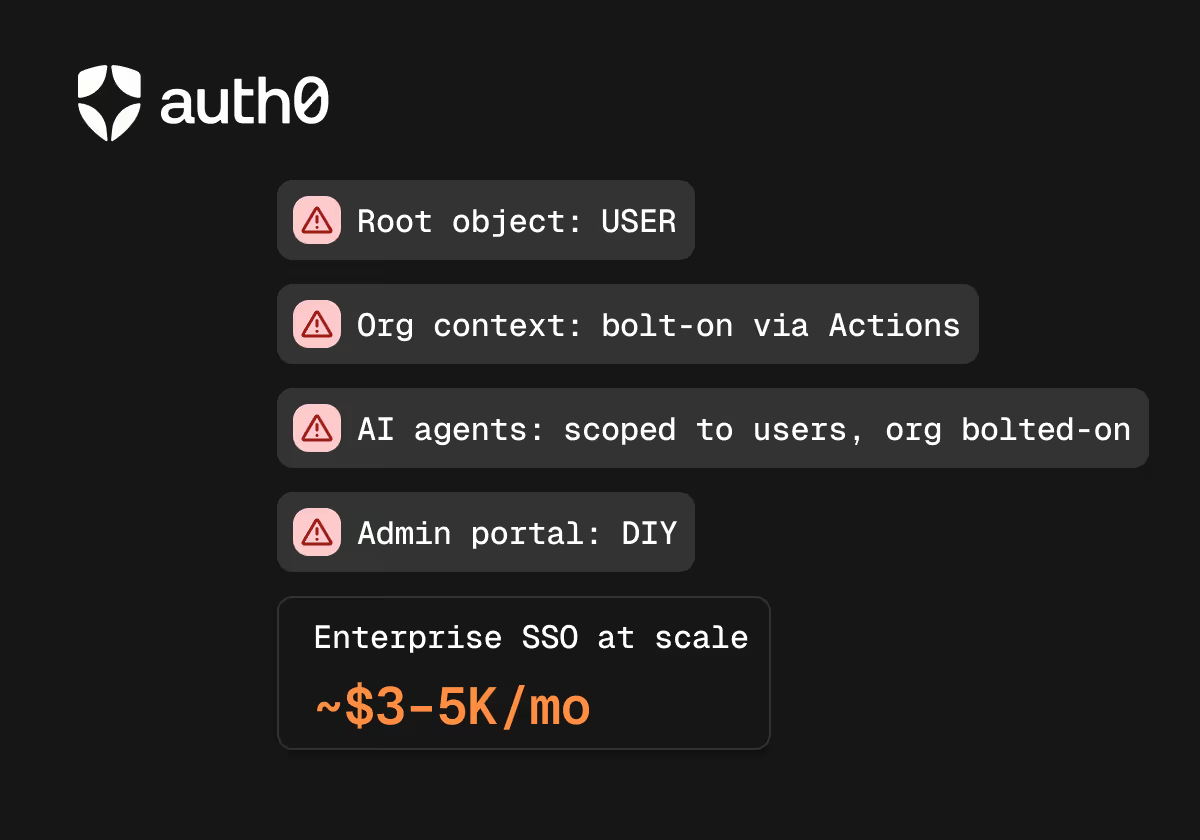
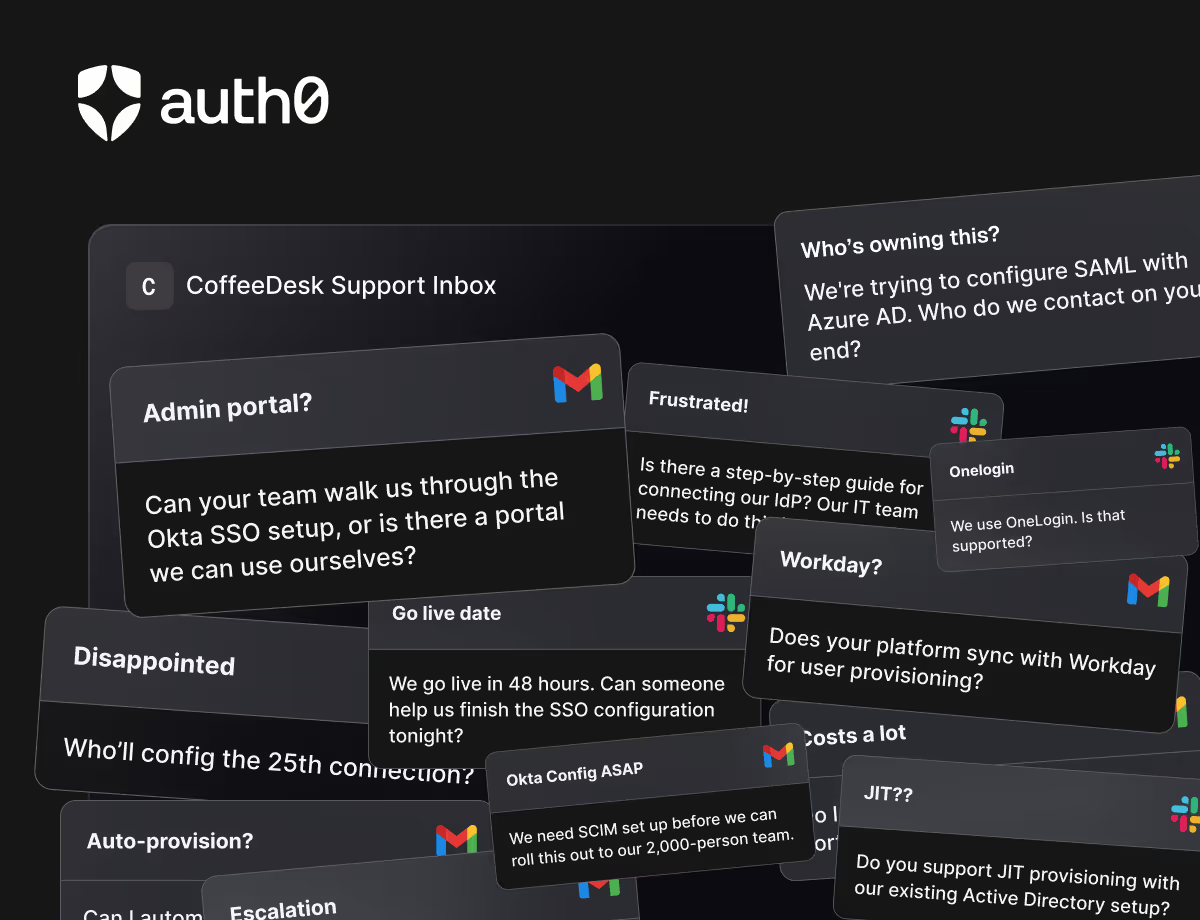
Yes, Auth0 supports both. In practice though, org context and policy enforcement are composed across Auth0 configuration, Actions, and application logic rather than enforced centrally. Role definitions are tenant-wide, not organization-scoped by default. As enterprise customers grow, SSO costs snowball quickly, and without a native admin portal, your team ends up doing hands-on configuration support instead of shipping product.
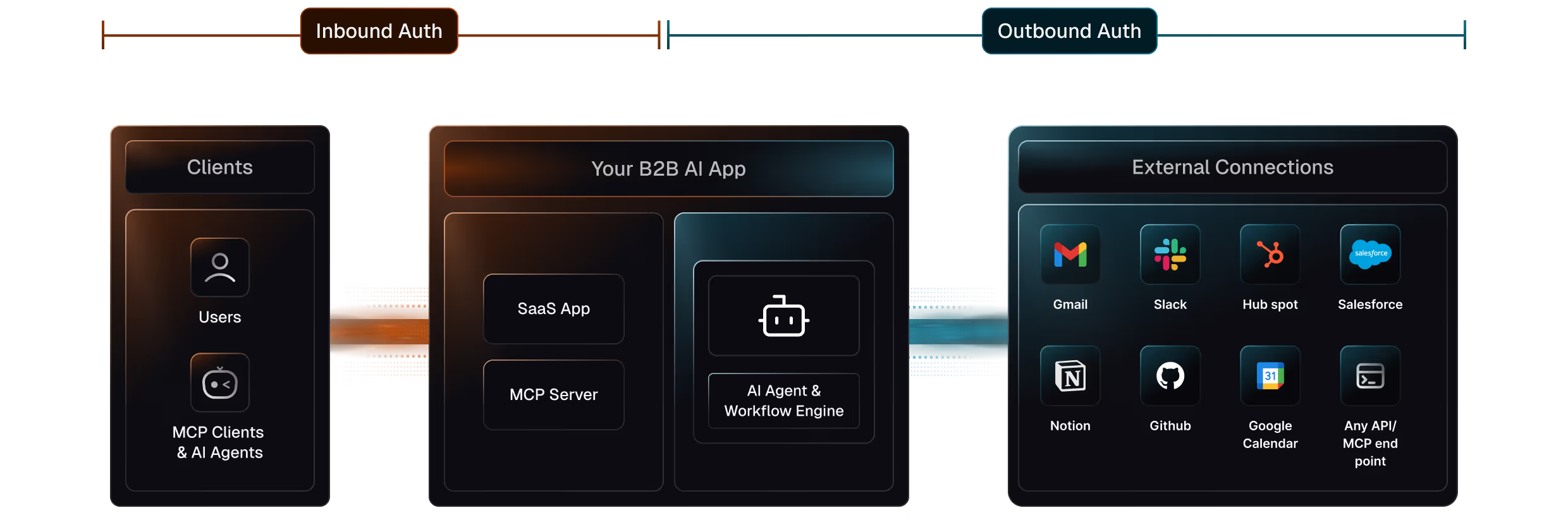
Teams rarely leave Auth0 because it broke. The trigger is usually a combination of a number of enterprise customers requiring SSO and SCIM, growing friction from reconstructing org context on every request, and new AI features introducing agents or service-to-service auth that Auth0 has no clean primitive for. Identity starts taking more engineering attention than it should. Not a crisis, but a steady accumulation of workarounds and reduced engineering bandwidth.