Frontegg Alternatives in 2026: Best Auth Platforms for B2B AI Apps

Frontegg built a well-rounded platform for a specific version of B2B SaaS: a product where the primary identity surface is user login, tenant management, and an admin portal. For that scope, it remains a capable choice. Teams can get hosted auth, SSO, SCIM, RBAC, and a self-service admin UI running quickly, without stitching together multiple tools.
What tends to shift the evaluation is product direction, not product quality.
B2B apps in 2026 increasingly ship features that require identity to stretch beyond user login: agents acting on behalf of users, MCP servers that expose product functionality to AI clients, and API flows that run without a human in the loop. When those surfaces appear, the identity layer needs to model humans, organizations, and machines under the same coherent system.
Frontegg's response to this has been additive: agent authentication lives in Frontegg, a separate product lives in AgentLink, another separate product. Each addresses the surface it was built for. What they don't do is unify into a single identity layer. Agent auth works for agents built on Frontegg. MCP auth works for AI clients that connect through AgentLink. If your agent is built on a different framework, or you want to expose your API to an external AI client like Claude or ChatGPT, you're operating outside the system's coverage.
The result is a platform that solves each problem individually but requires teams to manage those products as a stack rather than relying on identity as coherent infrastructure. For teams evaluating their options before that complexity accumulates, this page examines the alternatives.
The Comparison Scenario
All pricing estimates below use the same scenario for consistency:
A B2B AI app with 200 customer organizations, ~8,000 monthly active users, and 50 customers requiring enterprise SSO (and SCIM where supported).
Numbers are approximate and reflect published pricing tiers. They represent pricing behavior, not exact invoices or negotiated contracts.
Auth0
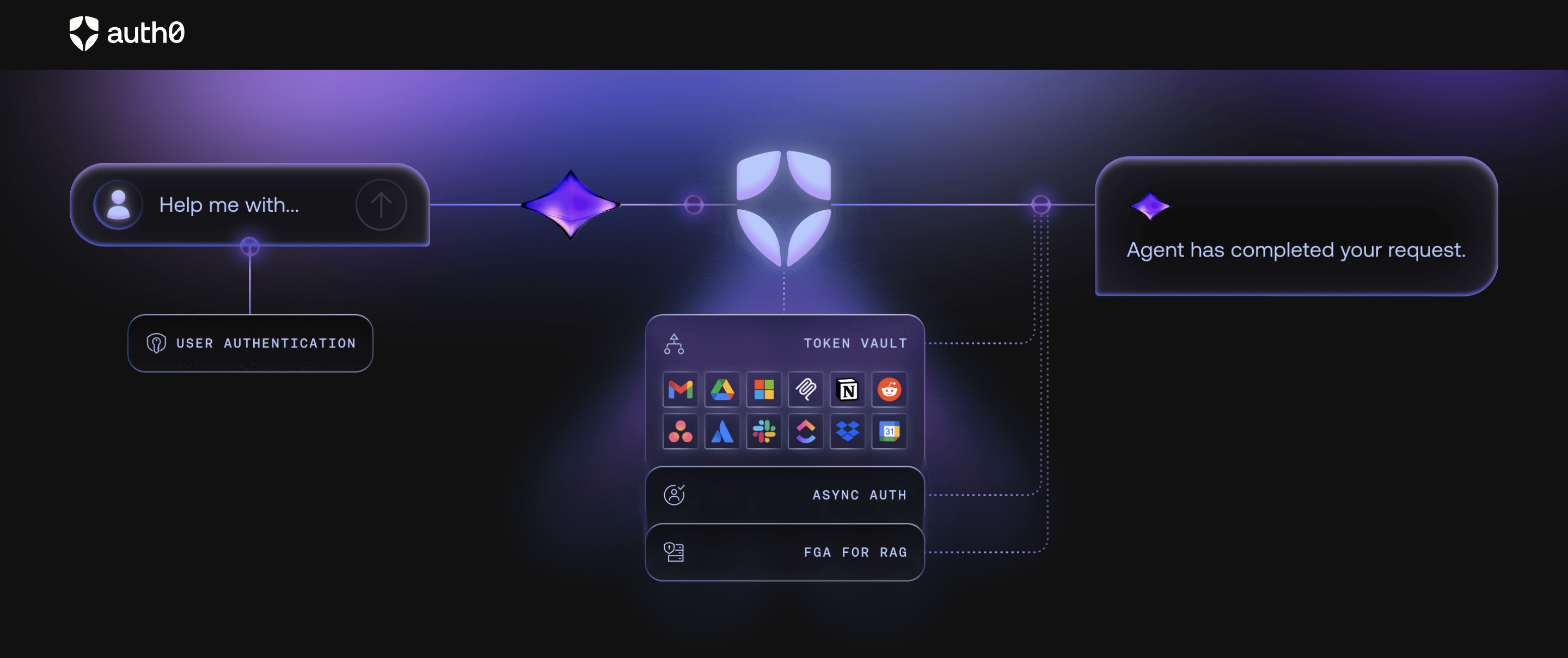
Auth0 is the category default for teams where compliance and enterprise trust are the primary buying criteria. The Okta acquisition brought SOC 2 Type 2, BAA support, and a compliance posture that opens doors in regulated industries like financial services, healthcare, and government. For teams that need identity to pass enterprise security reviews, Auth0 carries institutional credibility.
The architecture is user-first. B2B organizational modeling is available through Organizations and Actions, but it's layered on top of a user-centric model rather than native to it. As products mature, teams often find themselves reconstructing org context in application code, carrying tenant semantics through custom claims, and managing access control logic across multiple layers. Enterprise SSO and SCIM sit at higher tier levels, and dev environments are billed at production rates.
For teams where compliance posture is the overriding requirement and engineering capacity exists to manage the B2B modeling overhead, Auth0 is a defensible choice.
Pricing (based on the shared scenario):Auth0's B2B Identity add-on is required for per-org SSO at this scale. Estimated $1,500–$2,500/month depending on tier and negotiation.
Recommended Reading: Auth0 Alternatives for Agent Auth (AI-focused)
WorkOS
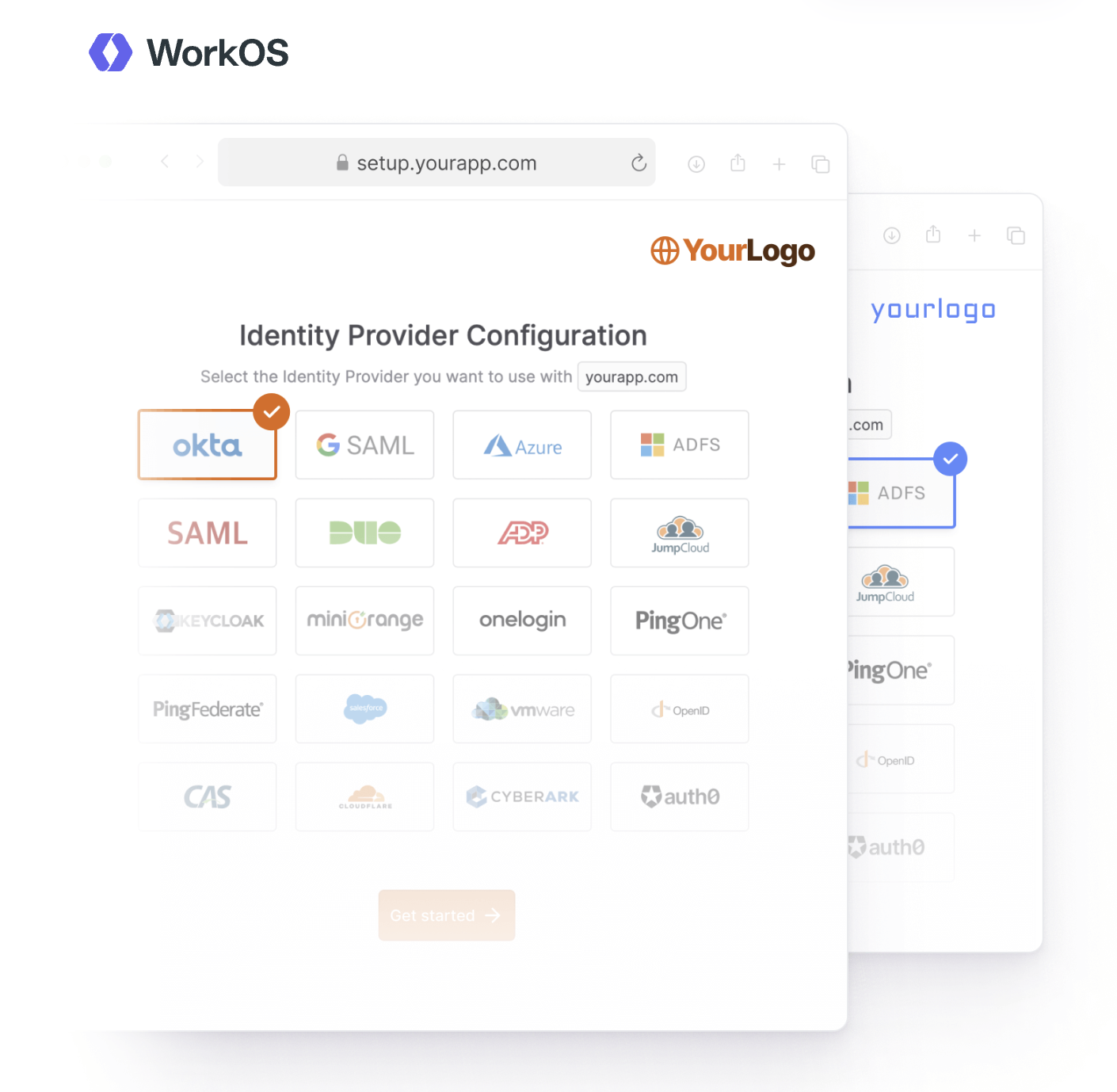
WorkOS made a deliberate architectural choice: focus exclusively on enterprise authentication capabilities — SAML SSO, SCIM provisioning, directory sync — and expose them as a clean layer. The result is a precise tool for a precise problem.
Teams that already have user auth (Auth0, Cognito, Clerk, or an in-house system) and need to add enterprise capabilities on top often find WorkOS is the path of least disruption. The Admin Portal is polished, the SAML implementation is thorough, and the developer experience reflects genuine product investment.
With time, AuthKit, MCP Auth and Pipes for Agent Connectors arrived but enterprise auth is their flagship focus. The deliberate limitation is also its architectural constraint: WorkOS doesn't unify identity entirely. That split is manageable until the product needs unified org-scoped tokens, agent identity, or a consistent control layer across human and non-human actors. As SSO connections scale, per-connection pricing compounds quickly.
Pricing (based on the shared scenario):Applying cumulative volume tiers for 50 SSO + 50 SCIM connections:
- SSO: 1–15 × $125 + 16–30 × $100 + 31–50 × $80 = $4,975/month
- SCIM: same slab structure = $4,975/month
Estimated monthly total: ~$9,950/month (excluding primary auth system cost)
Recommended Reading: WorkOS alternative, find what fits best in your stack
Clerk
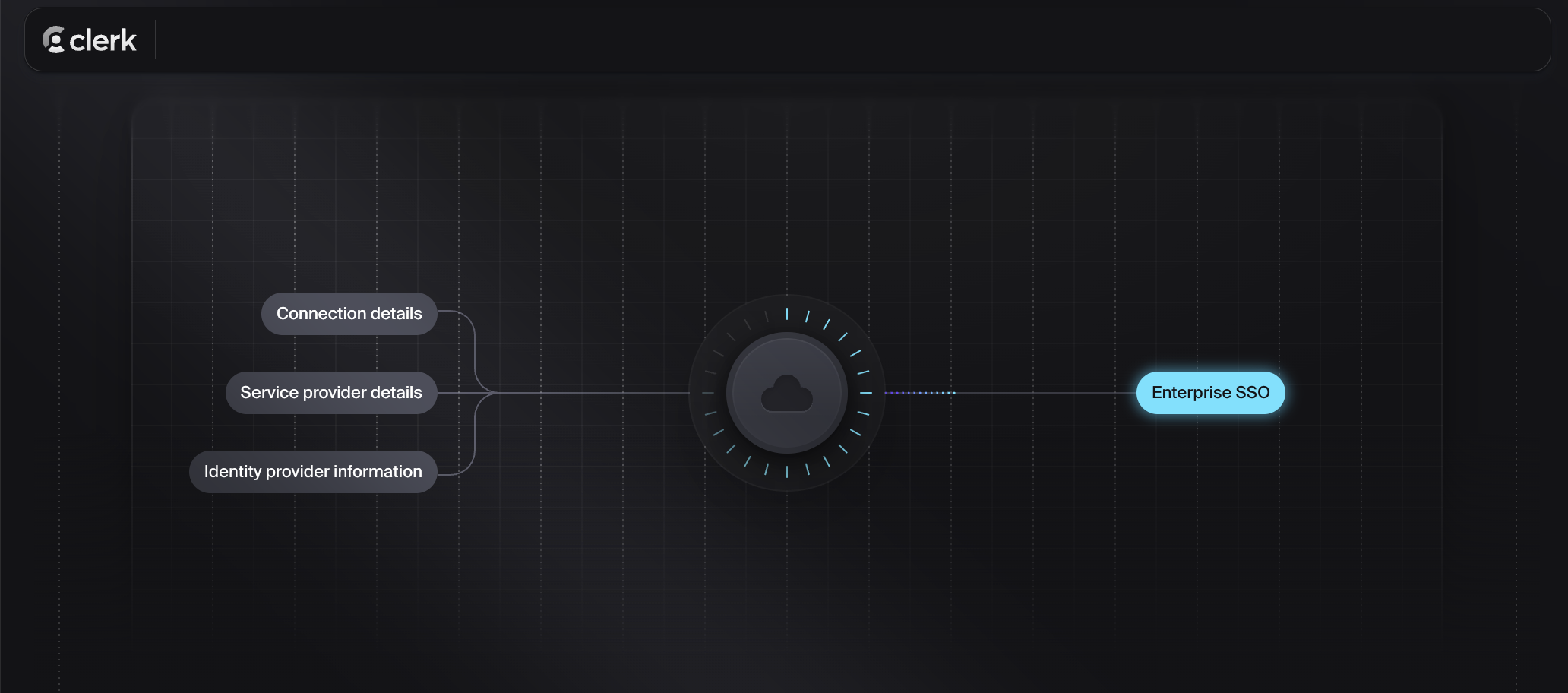
Clerk's developer experience for user authentication remains one of the strongest on this list. Drop-in React components, a fast path to a working login page, and SDK quality that most auth platforms don't approach. For teams with consumer-facing surfaces or early-stage products where authentication is primarily user-driven, Clerk gets to production fast.
The B2B org model has matured, but it was built onto a user-first foundation. Organizations in Clerk are groupings of users rather than the root identity boundary. SCIM provisioning is not natively supported. Fine-grained roles require the Enhanced Organizations add-on. Authorization beyond standard RBAC and non-user actors are not supported. Services, background jobs, agents typically live in application code.
Teams frequently find themselves building IdP discovery logic, tenant routing, and customer-facing admin flows on top of Clerk as enterprise requirements grow. Each addition is reasonable; together they represent identity logic that a purpose-built B2B platform handles natively.
Pricing (based on the shared scenario):Applying cumulative SSO slabs:
- Base Pro plan: $25/month
- MAUs: 8,000 × $0.02 = $160/month
- Enhanced Organizations add-on: $100/month
- SSO (50 connections): 1 included + 2–15 (14 × $75) + 16–50 (35 × $60) = $3,150/month
Estimated monthly total: ~$3,435/month (SCIM requires additional tooling outside Clerk)
Recommended Reading: Clerk Alternatives for B2B SaaS & AI Apps in 2026
PropelAuth
PropelAuth was designed for B2B SaaS from the ground up: org-native user management, hosted UIs for org administration, RBAC, invitations, and SSO without significant custom work. In terms of scope and intended use case, it's the most direct functional comparison to Frontegg on this list.
The trade-off is coupling. PropelAuth works well when teams adopt the full stack as intended. When requirements call for custom auth UI, selective integration with an existing system, or identity that extends beyond user-facing flows into API and agent access, the platform's opinions begin to constrain rather than accelerate. No documented model for agent auth or MCP server authentication.
For teams at early-to-mid scale with standard B2B SaaS requirements and limited need for modularity, it's one of the more economical full-stack options. But it is no longer the strongest fit for AI apps in 2026.
Pricing (based on the shared scenario):SSO and SCIM included in higher tiers. Estimated $300–$600/month at this scale.
SuperTokens
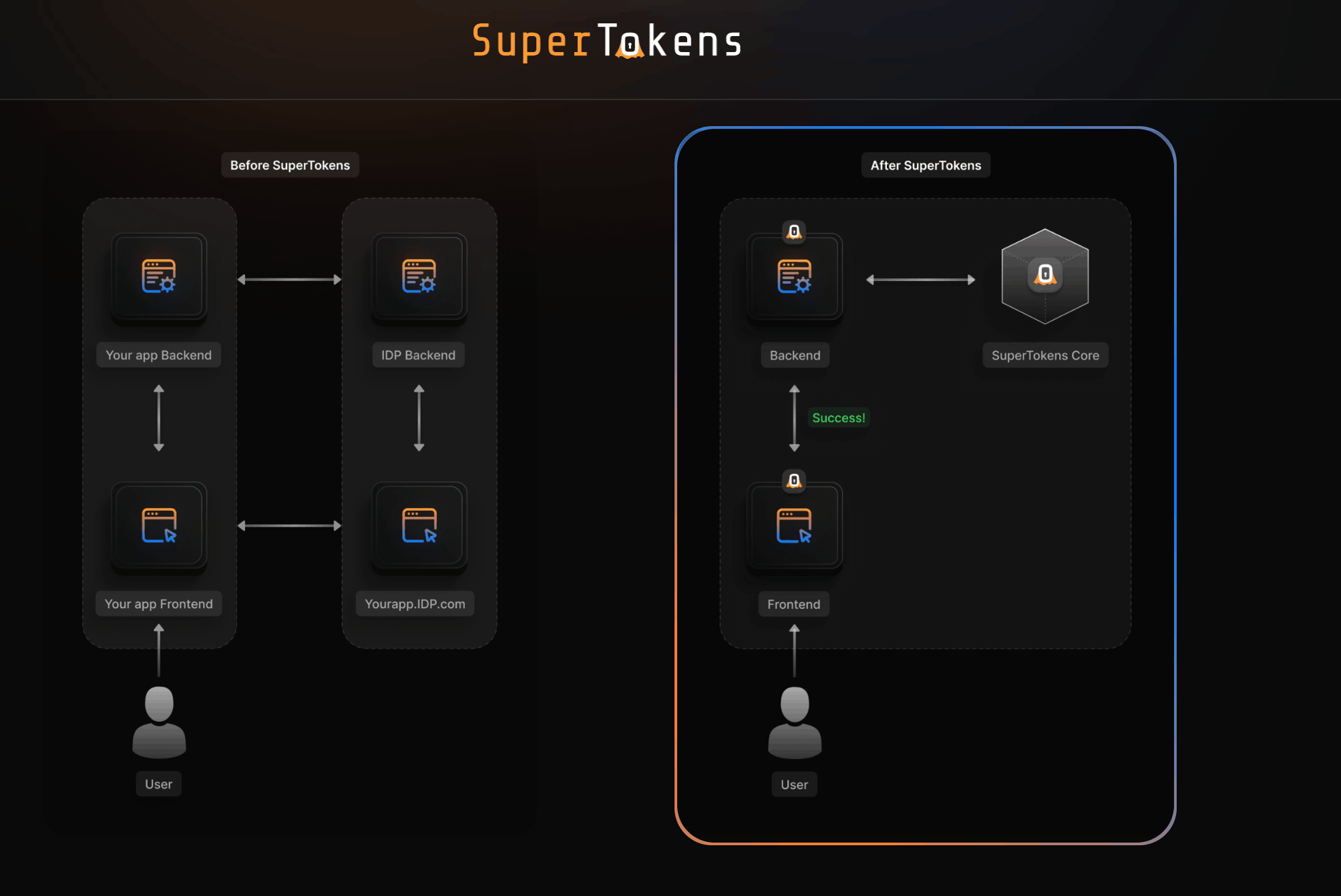
SuperTokens is open-source with a managed cloud option. It gives teams that want to own and audit their auth layer a credible path to doing so without starting from scratch. The ability to inspect, extend, and operate the codebase directly is a genuine differentiator for security-conscious teams.
The B2B multi-tenancy and enterprise features exist but lag behind commercial platforms. Building agent auth on top of SuperTokens requires custom implementation. Teams choosing SuperTokens are typically optimizing for ownership and auditability over enterprise feature completeness.
Pricing (based on the shared scenario):Self-hosted is free. Managed cloud at 8K MAUs with multi-tenancy: roughly $300–$500/month, with per-connection costs for SSO.
Ory
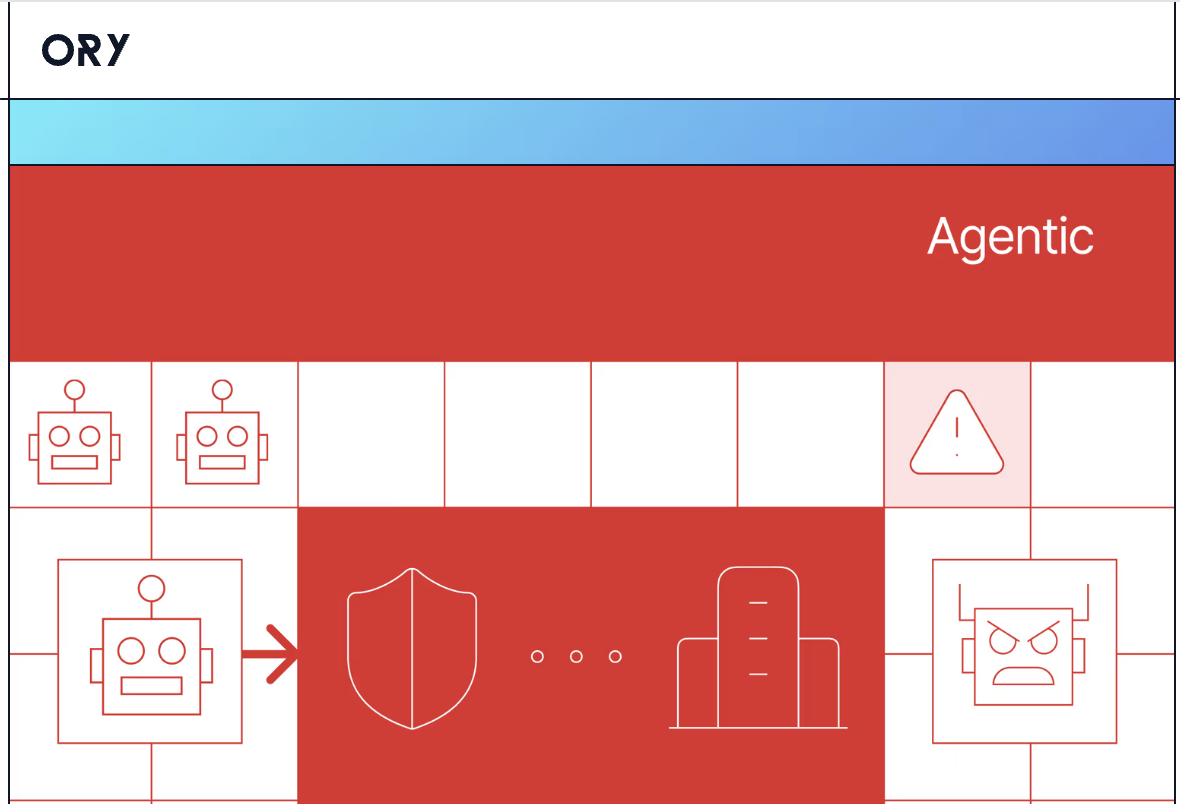
Ory is infrastructure-layer identity: open-source, composable, and designed for platform engineering teams that treat identity as something they operate rather than purchase. Hydra for OAuth2/OIDC, Kratos for user management, Keto for permissions — discrete components assembled by the team.
It offers the most control of anything on this list. It also requires the most to implement and maintain. B2B org workflows, enterprise SSO setup, customer-facing admin experiences, and non-human identity all require substantial custom work. This is the right choice for a specific set of teams — those with strong platform engineering capacity and a clear case for ownership — and the wrong choice for most.
Pricing (based on the shared scenario):Open-source license: $0. Ory Network pricing scales with usage; complex B2B deployments typically reach enterprise contracts. Engineering and operational cost is the dominant variable.
Descope

Descope's differentiator is its visual flow builder for authentication — login, signup, and MFA behavior configured through no-code and low-code tooling. That abstraction extends into AI identity: its Agentic Identity Hub (launched 2025, updated early 2026) covers MCP auth, OAuth 2.1, Dynamic Client Registration, tool-level scopes, and a credential vault for outbound connections to 50+ services. For teams that prefer configuring auth workflows visually rather than writing them, it's a distinctive option.
The caveat is the same across both human and agent auth: teams needing deep programmatic control may find the visual-first model limiting. The agentic features are newer and still building an enterprise track record.
Pricing (based on the shared scenario):Not fully public at this scale. Estimated $3,000–$4,000+/month (custom pricing) once SSO and MAU limits are exceeded.
Amazon Cognito
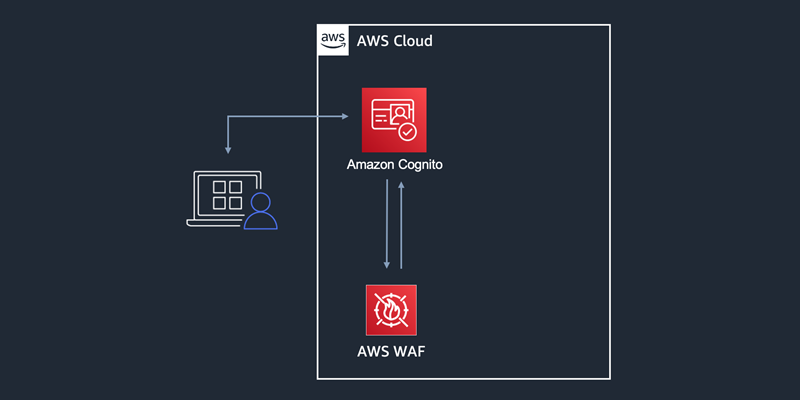
Cognito is the default for AWS-native teams. It integrates tightly with IAM, Lambda, API Gateway, and the broader AWS ecosystem, and the free tier (up to 50,000 MAUs) makes early cost minimal. For products deeply embedded in AWS infrastructure where auth is one component of a larger AWS-resident architecture, it's a natural fit.
The well-documented limitation is the absence of a native B2B org model. Multi-tenancy requires designing and maintaining it yourself — one User Pool per tenant, custom attributes, or application-layer logic. Enterprise SSO through federation is possible but requires custom integration work. The engineering cost of building org workflows on Cognito is the reason it generates more migration traffic toward purpose-built B2B identity platforms than any other vendor on this list.
Pricing (based on the shared scenario):At 8K MAUs, base auth cost is effectively $0. Org workflow implementation and ongoing engineering are the meaningful costs.
Recommended Reading: AWS Cognito Alternatives for B2B SaaS and Agentic AI Auth
Stytch
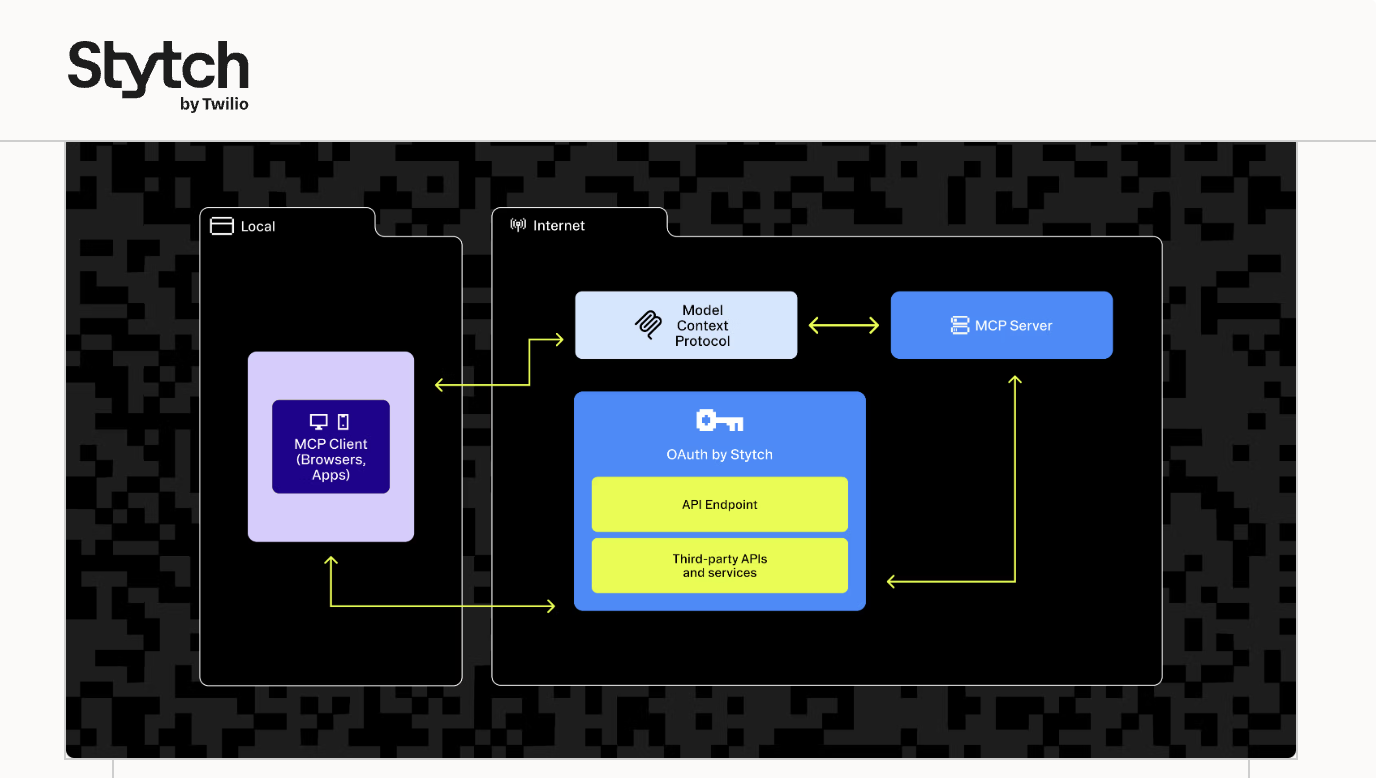
Stytch is an API-first B2B authentication platform built around Organizations and Members, with SSO, SCIM, RBAC, and a headless approach that suits teams building fully custom auth experiences. In 2025, it shipped Connected Apps — an add-on that handles OAuth 2.1 token lifecycle, consent UI, and MCP authorization for AI agents. It can be dropped into an existing auth stack without a full migration to Stytch.
A relevant context note: Stytch was acquired by Twilio in 2025. Some teams factor long-term product direction into their vendor evaluation.
Pricing (based on the shared scenario):
- MAUs: 8,000 × $0.20 = $1,600/month
- Enterprise connections (50 − 5 included): 45 × $125 = $5,625/month
Estimated monthly total: ~$7,225/month
Scalekit
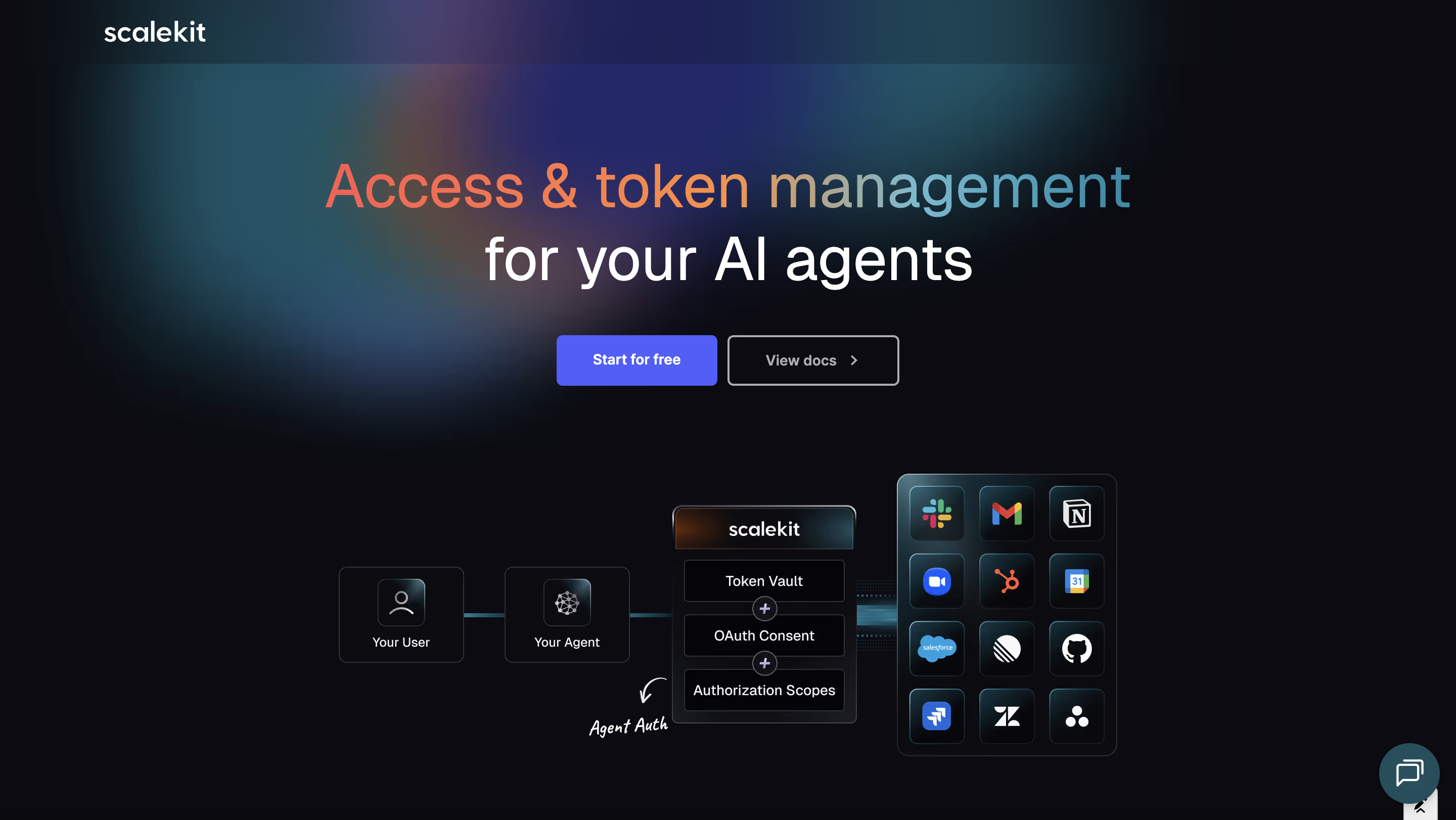
Scalekit is designed as an org-first identity layer for B2B products where identity needs to stay coherent as the product surface expands beyond user login. Organizations are the root identity object — users, machines, agents, and MCP clients are always resolved in the context of an organization. That's an architectural assumption, not a feature addition.
Three things are worth understanding specifically in the context of this comparison:
A unified identity layer, not separate product lines. SSO, SCIM, M2M auth, agent auth, and inbound MCP server authentication are all part of the same system and the same data model. When an agent acts on behalf of a user inside an org, the token reflects that natively. There is no separate product to configure for agents, and no coverage gap based on which framework the agent or AI client was built with. External AI clients — Claude, ChatGPT, Gemini — can authenticate to your MCP server through Scalekit's CIMD and dynamic client discovery support without any dependency on Scalekit's own stack.
Developer-native tooling. Scalekit ships its own MCP server, meaning developers can manage org configurations, test SSO connections, and inspect provisioning logs directly from Cursor, Windsurf, or any MCP-compatible IDE. Identity management moves into the development environment rather than requiring a separate dashboard context-switch.
Modular adoption path. Scalekit can function as a full identity layer or be introduced alongside an existing auth provider for specific capabilities — SSO first, then SCIM, then agent auth — without replacing production login infrastructure on day one. Teams that need to move carefully around existing systems can migrate capability by capability.
What to verify: Scalekit is a newer platform. TOTP-based MFA, SMS OTP, and adaptive risk-based MFA — areas where Frontegg has broader coverage — should be confirmed against current availability if they appear on your requirements list.
Pricing (based on the shared scenario):
- MAUs: first 1,000,000 included = $0
- Organizations: first 100 included, next 100 × $1 = $100/month
- SSO + SCIM connections (50 each, cumulative tiers):
- Connections 1–15: 15 × $60 = $900
- Connections 16–30 (25% discount): 15 × $45 = $675
- Connections 31–50 (40% discount): 20 × $35 = $700
- Total connections: $2,275/month
Estimated monthly total: ~$2,375/month
Pricing at a Glance
Scenario: 200 orgs, ~8,000 MAUs, 50 enterprise SSO connections
FAQs
As your product adds agents or exposes MCP servers, does your identity layer model them under the same org and policy system — or do they require a separate product?
The cost of managing separate products is low early and accumulates with scale.
If you expose product functionality via MCP, does your auth cover AI clients that weren't built on your identity vendor's stack?
Worth validating before committing to a vendor's MCP story.
How does your vendor price dev and staging environments?
Free environments affect experimentation velocity and onboarding in ways that don't appear in headline pricing comparisons.
Are you optimizing for where your product is now, or where it needs to be in 18 months?
Identity is one of the harder systems to migrate mid-scale. Teams that feel that friction most are typically the ones who built on a user-first platform and later needed to express org-first and execution-aware requirements.
Can your engineering team manage auth configurations from inside the IDE, or does every change require a context-switch to a dashboard?
The workflow difference compounds across a fast-moving team.













