Scalekit January roundup

We are kicking off 2026 with a set of updates focused on one theme: making authentication easier to adopt and easier to run, whether you are building an MCP server, shipping AI agent workflows, or supporting enterprise SaaS.
This post is a roundup of what’s new across MCP, agent authentication, and our developer experience.
MCP Auth: CIMD support for MCP servers
Client onboarding for MCP servers is now simpler. Scalekit supports Client ID Metadata Documents (CIMD), allowing MCP clients to identify themselves via a metadata URL instead of manual pre-registration.
This is designed for ecosystem-facing MCP servers with many independent or distributed clients, where pre-registering every client does not scale. CIMD can be enabled with a single setting in the dashboard.
If you want a deeper dive, watch our CTO Ravi, break down DCR vs. CIMD with Akshay (our in-house expert), who built the feature at Scalekit.
Read more about CIMD on the launch blog.
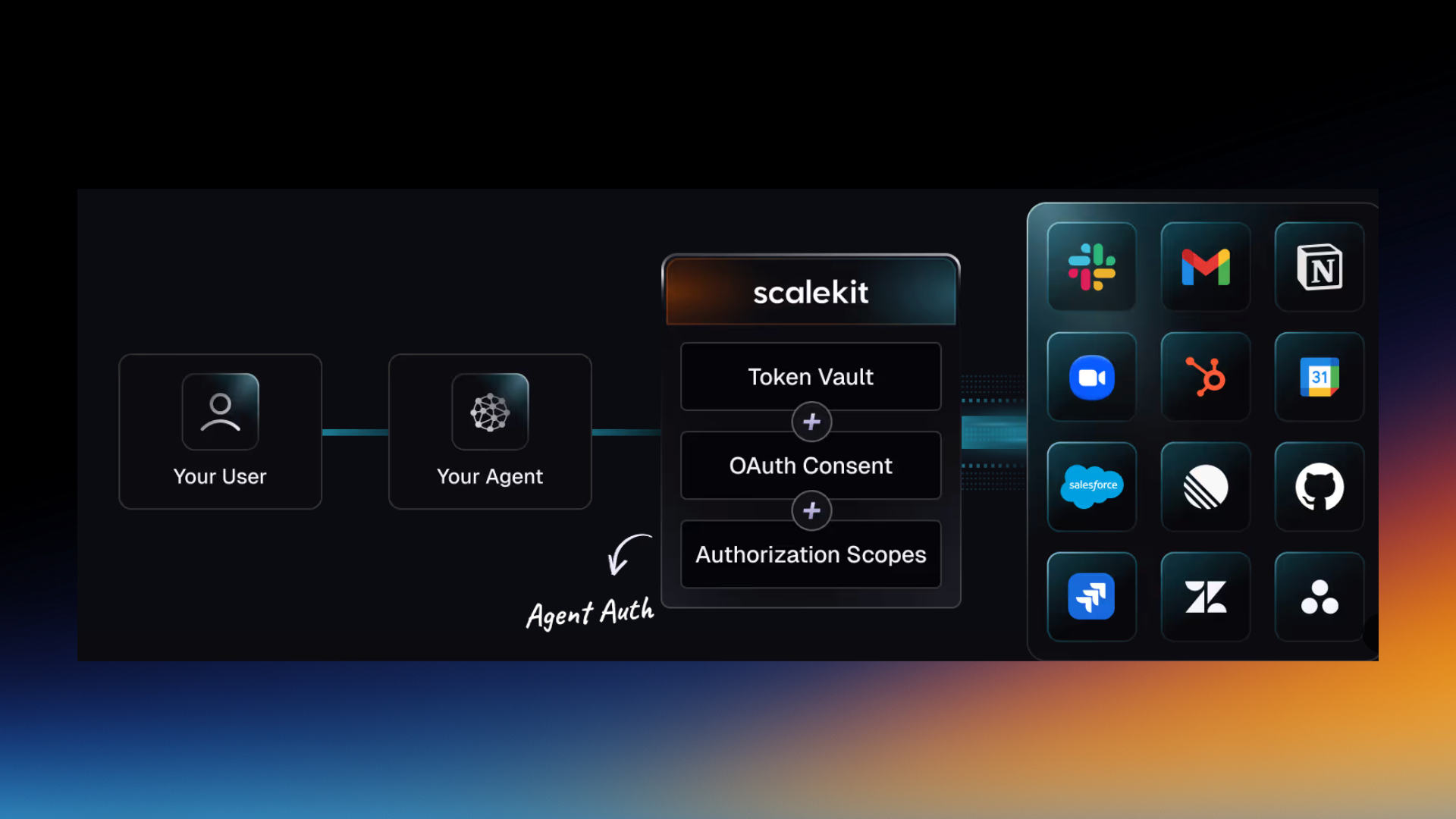
Agent Auth: A complete solution for Outbound Auth
We are also introducing Agent Auth: a complete solution for outbound authentication when AI agents interact with external systems. This includes agents acting on behalf of users, service accounts, and MCP tools.
Agent Auth includes:
- A token vault with automatic refresh, rotation, and lifecycle management
- Support for a wide range of connectors, with new additions like Google Meet, Google Sheets, Intercom, Monday, Airtable, ClickUp, Microsoft Excel, Word, OneDrive, and more
- Custom domains for branded consent flows
- Flexible authentication methods including OAuth 2.0, API keys, and custom JWTs
Agent Auth works across major agent frameworks and runtimes, so teams can standardize how outbound auth is handled as their agent architecture evolves.
Learn more about Agent Auth.
Full stack Auth: Enhancements
User provisioning via interceptors
You can now provision users programmatically during authentication, with control over user creation, attribute mapping, and organization assignment at auth time.
Get started here.
Passkeys SDK
The new Passkeys SDK lets you build fully custom Manage Passkeys screens while Scalekit handles the underlying security and protocol complexity.
Get started here.
Docs and developer experience
Choose Modular or FSA, upfront
We have restructured both the dashboard and the documentation to better reflect how teams actually build.
You now select your authentication mode upfront: go full-stack with everything integrated, or pick modular components like MCP Auth, Agent Auth, SSO, and SCIM. The documentation mirrors this structure, with use case-driven guides for MCP Auth, Agent Auth, and enterprise authentication, plus an end-to-end guide for using Scalekit as your complete auth layer. Go to Scalekit docs.
.gif)
Get faster starts with sample apps
Getting started is faster with forkable, real-world examples, including an end-to-end Coffeedesk implementation (Go + Node.js) and a separate Django Python implementation.These examples are designed to show realistic authentication flows, not just isolated snippets, so teams can adapt them directly into production codebases. Watch the Coffeedesk demo below. 👇 Or, check out sample apps here.
Ask AI on Scalekit docs
To make documentation more accessible, we also added Ask AI directly inside the docs. You can write questions in natural language and get clear answers in a few lines, without jumping between pages. Go to Scalekit docs.
These updates are aimed at giving teams clearer choices, fewer bespoke integrations, and a more predictable path from setup to production. If you are building with MCP, experimenting with AI agents, or rolling out enterprise features, we would love to hear what you are working on and where we can make things smoother.
FAQs
How does CIMD simplify client onboarding for MCP servers?
Scalekit simplifies the onboarding process for MCP servers by supporting Client ID Metadata Documents. This approach allows MCP clients to identify themselves through a metadata URL instead of requiring manual pre-registration. For engineering managers overseeing ecosystem facing servers with numerous distributed clients, this eliminates the scaling bottleneck associated with traditional methods like Dynamic Client Registration. By enabling this feature with a single dashboard setting, developers can facilitate secure automated client identification without the administrative overhead of managing every individual client registration manually, significantly speeding up the deployment of MCP based architectures.
What capabilities does Scalekit offer for outbound agent authentication?
Scalekit provides a comprehensive Agent Auth solution designed for AI agents interacting with external systems. It includes a secure token vault that automatically handles token refresh, rotation, and lifecycle management. The system supports various connectors like Google Workspace, Microsoft Office, and Airtable, ensuring agents can securely access data on behalf of users or service accounts. Architects can leverage custom domains for branded consent flows and support multiple authentication methods including OAuth 2.0 and API keys. This standardizes how outbound authentication is managed across diverse agent frameworks, providing a robust foundation for AI driven workflows.
Can I programmatically provision users during the authentication process?
Yes, Scalekit now supports user provisioning through interceptors, allowing you to create and manage users programmatically during the authentication flow. This feature gives engineering teams granular control over user creation, attribute mapping, and organization assignment at the precise moment of authentication. By using interceptors, CISOs and developers can ensure that user identities are correctly established and updated in real time, reducing the need for separate synchronization tasks. This streamlined approach simplifies the onboarding of new users into enterprise SaaS environments while maintaining strict control over how identity data is mapped and stored.
How does the new Passkeys SDK benefit developers?
The new Passkeys SDK is designed to help developers build fully custom Manage Passkeys screens while Scalekit manages the underlying security and protocol complexities. This allows engineering teams to offer a modern, passwordless authentication experience that aligns with their specific brand and user interface requirements. By abstracting the intricate details of FIDO2 and WebAuthn protocols, the SDK enables faster implementation of secure, phishing resistant authentication. Developers can focus on the user experience and front end design, confident that the backend security and cross platform compatibility are handled by Scalekits robust infrastructure.
Should I choose modular components or full stack authentication?
Scalekit now allows you to choose your authentication mode upfront based on your specific architectural needs. You can opt for a full stack approach where everything is integrated into a single cohesive system, or select specific modular components like MCP Auth, Agent Auth, SSO, or SCIM. This flexibility is ideal for teams that might already have an existing identity provider but need to add enterprise grade features or specialized agent authentication. By selecting the right mode in the dashboard, the documentation and configuration experience are tailored to your choice, ensuring a more efficient and relevant setup process.
Why is CIMD preferred over DCR for large ecosystems?
For ecosystem facing MCP servers with many independent or distributed clients, traditional Dynamic Client Registration often fails to scale efficiently. CIMD, or Client ID Metadata Documents, offers a superior alternative by allowing clients to identify via a metadata URL. This removes the need for the server to pre register and store credentials for every possible client in advance. For CTOs and architects, this means lower maintenance overhead and a more flexible trust model. It supports a decentralized environment where clients can be onboarded dynamically and securely, making it the preferred choice for massive, scalable AI and MCP implementations.
How does Scalekit manage token lifecycles for AI agents?
Scalekit includes a dedicated token vault within its Agent Auth solution to manage the entire lifecycle of authentication tokens. This system handles the automatic refreshing of expired tokens and the rotation of credentials to maintain a high security posture without manual intervention. For developers building AI agent workflows, this removes the complexity of writing custom logic for token storage and renewal. By ensuring that tokens remain valid and secure as agents interact with external tools and APIs, Scalekit provides a reliable infrastructure that prevents service disruptions caused by expired or compromised authentication credentials.
Are there production ready examples for implementing Scalekit?
Scalekit provides forkable, real world sample applications to help engineering teams get started quickly. These include the Coffeedesk implementation, available in Go and Node.js, and a comprehensive Django Python implementation. Unlike simple code snippets, these examples demonstrate end to end authentication flows, showing how Scalekit integrates into a full stack architecture. Developers can adapt these production grade examples directly into their own codebases, reducing the time spent on initial setup and ensuring that best practices for security and user experience are followed from the very beginning of the development cycle.
How can I quickly find answers within Scalekit documentation?
To enhance the developer experience, Scalekit has integrated an Ask AI feature directly into its documentation. This tool allows developers and architects to write questions in natural language and receive clear, concise answers in just a few lines. This eliminates the need to manually browse through multiple pages to find specific configuration details or architectural guidance. By providing immediate, relevant technical answers, the Ask AI tool helps teams resolve integration challenges faster and stay focused on building their core products, ultimately reducing the total time to production for authentication features.













